Asymmetric encryption, https, iOSAPP signature principle
Asymmetric encryption, https, iOSAPP signature principle data collection
Asymmetric encryption, https, iOS certificate
I have read some things about encryption, certificates, RSA, and https before, but I have never understood them clearly. I don’t understand them very clearly. I will sort them out today.
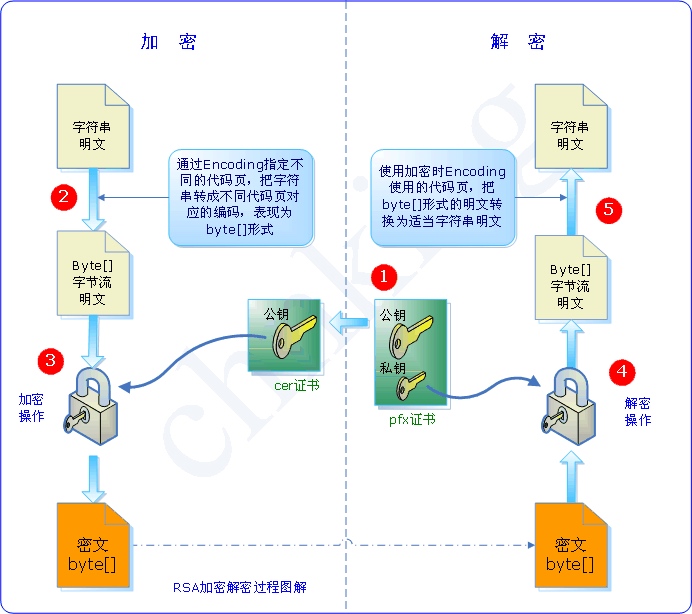
Encryption
The current encryption is divided into: 对称加密算法(symmetric key algorithms) and 非对称加密算法(asymmetric key algorithms)
In 对称加密算法, the key used for encryption and the key used for decryption are the same. In other words, the same key is used for encryption and decryption. Therefore, if the symmetric encryption algorithm wants to ensure security, the key must be kept secret and can only be known to the person using it and cannot be disclosed to the outside world.
密钥, generally a string or number, is passed to the encryption/decryption algorithm during encryption or decryption.
In 非对称加密算法, the key used for encryption and the key used for decryption are different.
So what are the differences between 对称加密算法 and 非对称加密算法 when used?
For example, this scenario:
Xiao Ming and Xiao Hong communicate with each other, but they don’t want others to know the content of the letter. Xiao Ming can use 对称加密算法 or 非对称加密算法 to encrypt the content.
If 对称加密算法 is used, since the key used for encryption and the key used for decryption are the same, how does Xiao Ming tell Xiao Hong the key?
Some people will say that if you re-encrypt the password, you still have to transmit the password, so there is always the problem of password leakage during the transmission process.
So what to do with 非对称加密算法?
First, Xiaohong generates the public key and private key, keeps the private key, and publishes the public key. Xiaoming uses the public key to encrypt the content of the letter, and then transmits the letter to Xiaohong. Since only Xiaohong has the private key, even if others intercept the content of the letter, they cannot crack it.
Because the private key does not need to be disseminated, it will not be intercepted by others due to dissemination.
The public key and private key in 非对称加密算法 appear in pairs. The public key and the private key are essentially equal, that is, two secret keys a and b are generated through an algorithm. When you publish a, a becomes the public key, and when b is published, b becomes the public key. Public keys and private keys are relative, and the two themselves do not specify which one must be the public key or the private key.
- Public key and private key appear in pairs
- The public key is called the public key, and the key that only you know is called the private key.
- Data encrypted with the public key can only be decrypted by the corresponding private key.
- Data encrypted with a private key can only be decrypted by the corresponding public key
- If it can be decrypted with the public key, it must be encrypted by the corresponding private key.
- If it can be decrypted with the private key, it must be encrypted by the corresponding public key.
Two usages of 非对称加密算法
- Achieve secure transmission of data To achieve secure transmission of data, of course the data must be encrypted. If you use a symmetric encryption algorithm and use the same key for encryption and decryption, in addition to saving it yourself, the other party must also know this key to decrypt the data. If you pass the key along with it, there is a possibility of password leakage. If we use an asymmetric algorithm, the process is as follows:
1. First, the receiver generates a pair of keys, namely private key and public key;
2. Then, the receiver sends the public key to the sender;
3. The sender uses the received public key to encrypt the data and then sends it to the receiver;
4. After receiving the data, the receiver uses its own private key to decrypt it.
Since in the asymmetric algorithm, the data encrypted by the public key must be decrypted with the corresponding private key, and the private key is only known by the recipient himself, thus ensuring the security of data transmission.
-
Digitally sign information In addition to ensuring the secure transmission of data, another use of the public key system is to sign data. Typically “digital signatures” are used to verify the identity of the sender and help protect the integrity of the data.
For example: a sender A wants to send some information to everyone, and uses his own private key to encrypt the information, that is, to sign. In this way, everyone who receives the information can use the sender’s public key to verify and confirm that the information was sent by A. (Because only the information obtained by A using the private key signature can be decrypted with this public key) Using digital signatures, two points can be confirmed:
- Ensure that the information is signed and sent by the signer himself, and the signer cannot deny or find it difficult to deny.
- It is guaranteed that the information has not been modified in any way from the time of issuance to the time of receipt. The reason why these two points can be confirmed is that what can be decrypted with the public key must be encrypted with the corresponding private key, and the private key is only held by the signer.
Note: Digital signatures use private keys, and information encrypted with private keys is called digital signatures, because the private keys are only held by you, which is equivalent to an official seal. The private key used for digital signature is just like the steel seal on a graduation certificate. Only a certificate with a steel seal will be recognized as genuine.
So can you use a public key for digital signature? Because the public key is public and available to everyone, it makes no sense to use the public key for digital signatures. Conversely, can the private key be used to encrypt data to achieve secure data transmission? The answer is no, because the public key is public and can be obtained by everyone, and everyone can decrypt the information encrypted by the private key.
Let’s organize it again: Two secret keys are generated through the algorithm, one is made public and is called the public key; the other is kept by oneself and is called the private key; the information is encrypted by oneself and released, which is called a digital signature, because only the public key corresponding to the private key (equivalent to the official seal) can be decrypted. Those who can decrypt naturally know that only I can send this information, which ensures the publisher of the information.
Others use the public key to encrypt information, and only I can decrypt it, because I have the private key, which enables secure transmission of data.
Having said so much, I wonder if you understand the relationship and use of public keys and private keys?
The following content is excerpted from other articles and may also help you understand:
If you just use the asymmetric encryption algorithm unilaterally, there are actually two ways for different purposes:
The first is a signature, which uses private key encryption and public key decryption. It is used to allow all public key owners to verify the identity of the private key owner and to prevent content published by the private key owner from being tampered with. However, it is not used to ensure that the content is not obtained by others.
Anyone with the sender's public key can verify the correctness of the signature.
The second type is encryption, using the public key to encrypt and the private key to decrypt. Used to publish information to the public key owner. This information may be tampered with by others, but cannot be obtained by others. If A wants to send a secure and confidential data to B, then A and B should each have a private key. A first uses B's [public key] to encrypt the data, and then uses his own private key to encrypt the encrypted data. Finally, it is sent to B, which ensures that the content will not be read or tampered with.
Anyone who knows the recipient's public key can send a message to the recipient.
Summary: Public keys are commonly used to encrypt messages and verify digital signatures (i.e., decrypt).
1. Digital signature
Digital signature technology is the application of two technologies: "asymmetric key encryption and decryption" and "digital digest". It encrypts the digest information with the sender's private key and transmits it to the recipient together with the original text. The receiver can only use the sender's public key to decrypt the encrypted summary information, and then use the HASH function to generate a summary information for the received original text, which is compared with the decrypted summary information. If they are the same, it means that the received information is complete and has not been modified during the transmission process. Otherwise, it means that the information has been modified, so the digital signature can verify the [integrity] of the information.
The process of digital signature is as follows: plain text --> hash operation --> summary --> private key encryption --> digital signature
The process of digital signature verification is as follows: digital signature --> public key decryption --> summary --> hash original text --> comparison summary
Digital signatures have two functions:
Make sure that the message is indeed signed and sent by the sender, because others cannot forge the sender's signature. (Reliable source)
Make sure the message is complete and has not been tampered with (integrity).
Note: Digital signatures can only verify the integrity of the data. Whether the data itself (i.e. the original text) is encrypted is not within the control scope of the digital signature.
digital signature
Now that we know there is asymmetric encryption, what about digital signatures?
The function of a digital signature is that I mark a certain piece of data to indicate that I approve the data (signed my name), and then I send it to others. Others can know that the data has been authenticated by me and that the data has not been tampered with.
These articles can also help you understand: Cryptozoology Notes: http://www.ruanyifeng.com/blog/2006/12/notes_on_cryptography.html What is a digital signature? : http://www.ruanyifeng.com/blog/2011/08/what_is_a_digital_signature.html RSA algorithm principle (1): http://www.ruanyifeng.com/blog/2013/06/rsa_algorithm_part_one.html Understanding public and private keys: https://songlee24.github.io/2015/05/03/public-key-and-private-key/ Public keys, private keys and digital signatures are best understood like this: https://blog.csdn.net/21aspnet/article/details/7249401
https and man-in-the-middle attacks
The https protocol is the http+ssl protocol. The connection process is shown in the figure below:
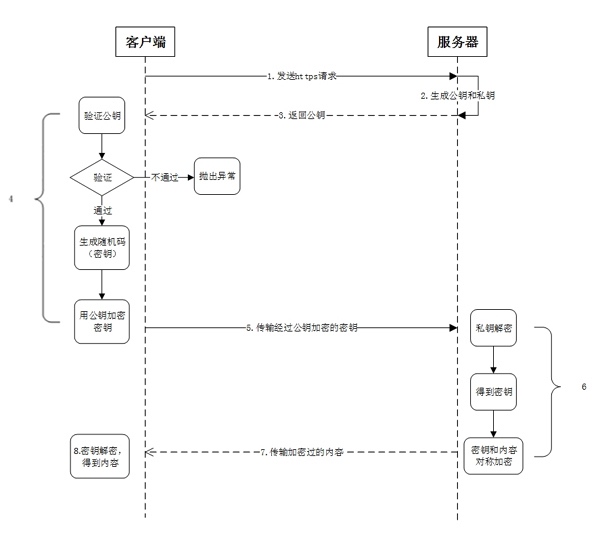
Take a look at this article specifically: HTTPS connection process and man-in-the-middle attack hijacking: http://netsecurity.51cto.com/art/201712/559836.htm In-depth HTTPS Series 2 (Encryption & Certificate): https://www.jianshu.com/p/b4c775a26068 HTTP, HTTP2.0, SPDY, HTTPS Some things you should know: http://web.jobbole.com/87695/
The principle of iOS certificate and App signing
After understanding the above points, it is simple to understand the principles of iOS certificates and App signing. If you don’t understand what’s above, you probably don’t understand what’s below either.
These two articles have made it very clear: How to understand the signing certificate mechanism of iOS: https://blog.gocy.tech/2017/04/24/iOS-Signing/ The principle of iOS App signature: http://wereadteam.github.io/2017/03/13/Signature/
读完之后,下一步看什么
如果还想继续了解,可以从下面几个方向接着读。